Honeypot & Sandbox
Honeypot
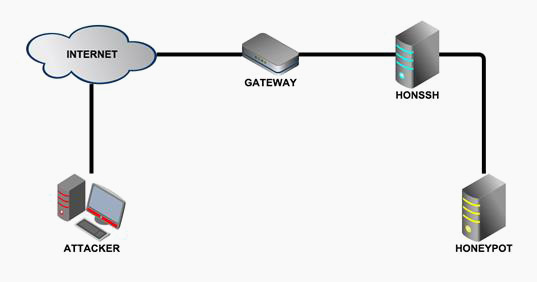
It is called a honeypot software or set of computers intended to attract attackers, pretending to be systems vulnerable or weak to attacks. It is a computer security tool used to collect information about the attackers and their techniques. Honeypots can distract attackers from the most important machines in the system, and promptly warn the system administrator of an attack, in addition to allowing an in-depth examination of the attacker, during and after the honeypot attack. There are low interaction honeypots, used primarily as a security measure, and high interaction honeypots, capable of gathering much more information for research purposes.
Sandbox
It is a process of separation of environment, that is, any computer is isolated, in order that said execution is safe to test without affecting the rest of the system, in case it was infected with any malicious software. It is extremely useful in computer security, since they allow us to execute and evaluate programs downloaded from the internet without compromising our computer against any type of malware. This isolated environment allows you to closely monitor the resources provided to the client programs to be executed, such as temporary space on disks and memory. Network access capabilities, the ability to inspect the host machine, and input devices, among others, are usually restricted. In this sense, process isolation is a specific example of virtualization.